Access The Dark Web
The dark web is a hidden portion of the internet not indexed by standard search engines, requiring specialized software to enter. Accessing the dark web often involves the Tor Browser, which routes your traffic through multiple layers of encryption to obscure your identity and location. While the technology is legal, accessing the dark web comes with significant risks, including exposure to illicit content, malware, and surveillance. This article outlines the technical steps and precautions for accessing the dark web safely.
Prerequisites for Dark Web Access
Before you attempt access the dark web, ensure you have a secure baseline. Use a reliable VPN service to add an extra layer of encryption before launching Tor, as it masks your IP address from the entry node. Accessing the dark web without a VPN can expose your home network to malicious actors. Additionally, disable JavaScript in the Tor browser—this prevents potential exploits embedded in .onion sites.
Step-by-Step Guide to Access the Dark Web
To start accessing the dark web, download the official Tor Browser from the Tor Project website. Avoid third-party mirrors. After installation, launch the browser and configure the connection settings if you are in a region with censorship. Accessing the dark web requires patience; the Tor network can be slow due to its routing process. Once connected, navigate to a directory like The Hidden Wiki to find .onion links, but verify each site’s legitimacy.
Risks and Legal Considerations
While accessing the dark web is not illegal in most jurisdictions, many activities on it are prohibited. Law enforcement actively monitors Tor exit nodes, and accessing the dark web for illegal purchases or hacking services can lead to prosecution. Malware is rampant; avoid downloading files or clicking on unknown links. Access the dark web only for privacy-focused research or communication, such as using encrypted email services like ProtonMail.
Best Practices for Secure Access
When you access the dark web, never use personal information like real names or email addresses. Create pseudonymous accounts for any required registrations. Accessing the dark web with a dedicated device or a live operating system like Tails adds security by leaving no trace on your hard drive. Regularly update the Tor Browser to patch vulnerabilities. Remember: accessing the dark web is a tool, not a playground—proceed with caution.
- Several dark web search engines have been developed to index and provide access to hidden services.
- A part of the deep web, the dark web is also intentionally hidden and requires software like Tor in order to access it.
- The Tor Project says that of the 2 million people using Tor every day, only 1.5% of them are accessing hidden or dark websites (that’s 30,000 people).
- Tor’s onion routing method reroutes your data through a series of independent nodes.
- Clicking on the wrong link or downloading files on the dark web exposes you to the risk of ransomware, spyware, phishing scams, and data breaches.
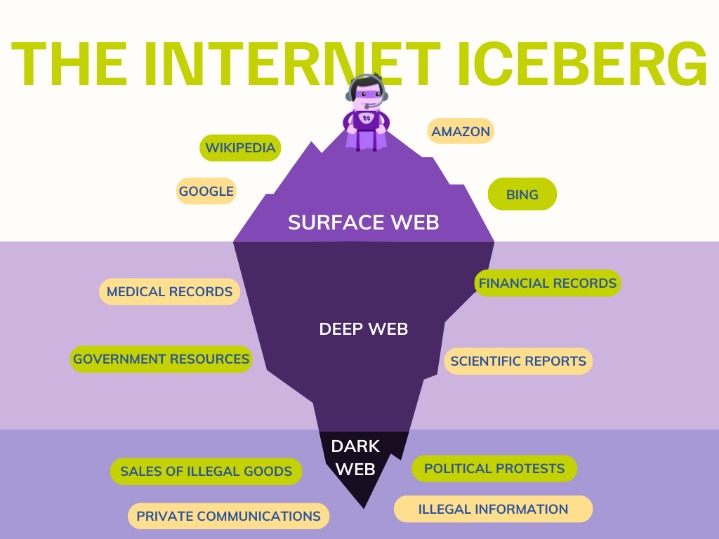
Instead, it encompasses all content on the internet that is not indexed by traditional search engines, making it inaccessible through simple search queries. These websites and services are typically identified by their unique .onion domain extensions, designed to conceal the actual location and identity of the website’s operators. The dark web is a network of hidden websites and services that operate on specialized software and protocols, such as the Tor browser. It is a part of the deep web, which encompasses all the content on the internet that is not indexed by search engines and inaccessible through standard search queries. If you want to view archived content (pages or whole websites that are no longer “live” online), the Wayback Machine stores older versions of many websites.
- Torch is one of the oldest and largest dark web search engines.
- These are sites that require login or subscription services to access, such as academic journals, court record databases, or even services like Netflix.
- The TOR browser provides improved privacy and anonymity on the public Internet and makes it possible to access .onion sites on the Dark Web.
- Tor is a web browser that lets you stay anonymous online or access the dark web.
- Even commerce sites that may have existed for a year or more can suddenly disappear if the owners decide to cash in and flee with the escrow money they’re holding on behalf of customers.
- To access the dark web, a special software or client is needed.
Often used to access the dark web, Tor Browser hides IP addresses and browsing activity by redirecting web traffic through a series of different routers called nodes. Tor (The Onion Router) is a web browser that lets users access a network that anonymizes web traffic to provide private web browsing. Law enforcement agencies keep an ear to the ground on the dark web looking for stolen data from recent security breaches that might lead to a trail to the perpetrators. Medical records, fee-based content, membership websites, and confidential corporate web pages are just a few examples of what makes up the deep web. Deep web refers to anything on the internet that is not indexed by and, therefore, accessible via a search engine like Google.