Access To Dark Web
The dark web, a hidden segment of the internet not indexed by standard search engines, is often shrouded in mystery and misconception. Accessing it requires specialized software, configurations, and a fundamental understanding of network anonymity. While frequently associated with illicit activities, its architecture also serves legitimate purposes, such as protecting whistleblowers and journalists in oppressive regimes. This article explores the technical pathways and considerations for accessing the dark web legally and safely.
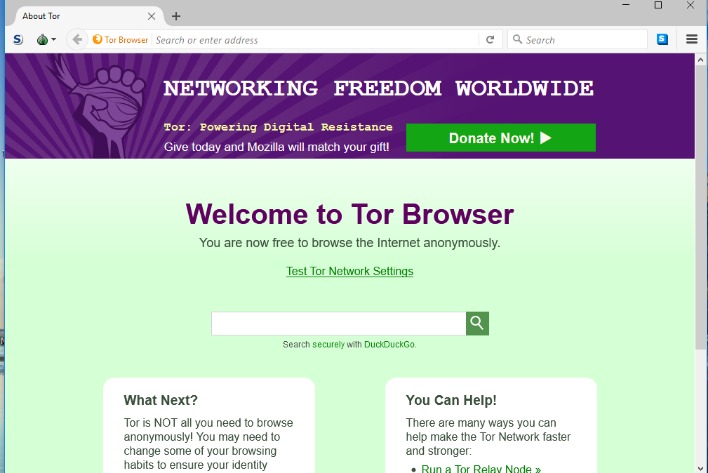
It requires a special browser called Tor to access it, and it allows visitors to remain anonymous. When accessing the dark web, you can only use a secure browser (which is also called an onion browser). Assess every website you visit for threats and security holes. As previously mentioned, more than 90% of the traffic on the internet is already on the deep web, so the keys to accessing it safely are virtually the same as the keys to accessing the open web safely. For this reason, dark web monitoring is critical for security.
Essential Tools for Entry
To reach the dark web, you cannot use a regular browser like Chrome or Safari. The primary gateway is through anonymity networks. Below are the core methods:
- Tor Browser: The most common tool. It routes your traffic through multiple encrypted relays, hiding your IP address. Download it only from the official Tor Project website.
- I2P (Invisible Internet Project): An alternative network focused on peer-to-peer communication and internal services, offering stronger anonymity for specific use cases.
- Freenet: A decentralized censorship-resistant platform for publishing and retrieving data, often used for forums and file sharing.
Step-by-Step Access Process
Accessing the dark web is not a single click process. It requires careful preparation to minimize risk.
- Install a VPN first: Connect to a reputable VPN provider that does not keep logs. This encrypts your traffic before it reaches the Tor network, adding a layer of privacy from your Internet Service Provider (ISP).
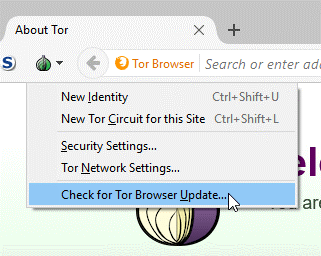
- Download and run Tor Browser: Never use a modified or third-party version. Ensure the browser’s security settings slider is set to “Safest” for maximum protection.
- Find .onion links: Unlike the surface web, dark web addresses use the .onion domain. Valid directories can be found on forums like Dread or through encrypted link lists, but be cautious—many are deceptive or malicious.
- Disable scripts and plugins: In Tor Browser, disable JavaScript by default via the NoScript add-on. Do not install Flash, QuickTime, or other ActiveX controls.
Common Risks and Precautions
- In a digital era where cyber threats constantly evolve, staying one step ahead is imperative for organizations aiming to safeguard their operational integrity.
- Below, we delve into the differences between the deep web and dark web, covering how to access them, their purposes, legal aspects, typical users, risks, browser options, use cases, and notable examples.
- This includes email accounts, private databases, paywalled sites, and subscription services.
- The dark web can be intriguing, but given its nature, you must stay vigilant and aware of the potential threats.
- KELA combines automated and human intelligence to detect cyber threats before they strike.
Navigating the dark web is inherently dangerous. Security must be prioritized over curiosity.
- Examples of deep web content include personal email accounts, university intranets, and corporate databases.
- A user can only access their information using the voter lookup tool available on the Surface Web.
- This hidden segment offers privacy and anonymity but also presents significant risks that necessitate robust dark web cybersecurity measures.
- Dark web forums serve as hubs for cybercriminal activity due to their anonymity, facilitating the exchange of stolen data, malware, and attack tools.
- Stolen online bank account access or credit cards may be traced on the dark web.
- Malware and Phishing: Many sites are designed to infect your device or steal credentials. Never download files from untrusted sources.
- Law Enforcement Monitoring: Authorities actively monitor high-profile dark web markets. Accessing illegal services can lead to investigation, even if you are just browsing.
- Exit Node Vulnerabilities: While Tor encrypts traffic within its network, the exit node can see your unencrypted data if the website is not HTTPS. Always check for the padlock icon.
- Personal Identification: Never use your real email, name, or payment information. Use cryptocurrency and disposable accounts for any interaction.
Legal and Ethical Boundaries
Accessing the dark web itself is not illegal in most jurisdictions, but what you do there is subject to local laws.
- Legal Uses: Bypassing censorship, secure communications, academic research, and accessing privacy-focused libraries.
- Illegal Activities: Buying drugs, weapons, stolen data, human trafficking, or engaging in fraud. These actions carry severe penalties.
Frequently Asked Questions (FAQs)
Can I access the dark web on my phone?
Yes, but it is riskier. The Orbot and Tor Browser apps for Android are available, but iOS devices have more limited security. Mobile use is discouraged for sensitive activities due to weaker sandboxing.
Is using a VPN necessary with Tor?
It is highly recommended. While Tor hides your destination, a VPN hides your Tor usage from your ISP. Some argue this can create trust issues with the VPN provider, but for basic privacy, it is the safer path.
What does ‘.onion’ mean?
It is a special-use top-level domain suffix designating an anonymous hidden service reachable only via the Tor network. These addresses are cryptographic hashes, making them difficult to remember or guess.
Will accessing the dark web slow down my internet?
Significantly. Tor routing through multiple relays creates high latency. Speeds are comparable to dial-up for many tasks. Do not expect streaming or large downloads.
How do I stay anonymous on the dark web?
Use a combination of a VPN, Tor Browser, disable all scripts, never log into personal accounts, and use a dedicated operating system like Tails (The Amnesic Incognito Live System) that leaves no trace after shutdown.


