Following deliberately crafted protocols that weigh legal, security, and operational considerations beforehand will discourage rash decisions that could put an organization, its employees, and its data in jeopardy. First, having a set of written guidelines in a dark web access policy will help keep your research efforts focused and within the bounds of your organization’s risk appetite. However, using Tor without additional protections could leave your device and network vulnerable to a cyberattack—and could attribute your activity back to you or your organization. The dark web’s popularity among criminals is why it’s so often useful to open-source intelligence (OSINT) investigations concerning cyberthreats, financial crime, fraud, human trafficking, child abuse, terrorism and narcotics. The dark web network infrastructure enables multi-layer encryption to prevent location tracking and preserves confidentiality among dark web users and hosts.
- Regardless of whether you use a virtual machine, it’s also important to conceal your identity.
- Freenet was introduced in 2000 as a research project aimed at building a censorship-resistant information network.
- Choosing the right Cyber Threat Intelligence platform can be the best weapon to win the war and protect your organization and customer data.
- These sites use “.onion” domains, which are made up of random letters and numbers up to 56 characters long.
- The Hidden Wiki isn’t a search engine, it’s a directory.
Their onion service provides the same privacy-respecting search without logging queries or tracking users. Dark web search engines help locate leaked files and database dumps. Criminals sell network access and trade stolen data on dark web forums. They run crawlers inside the Tor network and index .onion sites.
You can access most of the deep web using a normal browser. We’ll also discuss why it’s dangerous and why you should inform yourself about the dark web even if you don’t plan to be on it. If your mission depends on timely, credible, and safe dark web intelligence, it’s time to integrate dark web OSINT into your workflow. But that doesn’t mean it’s impossible to find and take down the bad guys. CluesAI works by scanning relevant records and revealing relationships between data points like usernames, contact information, cryptocurrency wallets, and more.
- Expanding their reach – through the use of Dark Web monitoring tools – can be invaluable to a corporate cybersecurity and risk management program.
- Try it for free now and protect your mobile data effectively!
- It comprises websites and resources indexed by search engines like Google, Bing, or Yahoo.
- Each of the following websites offers different services, from marketplaces to secure communication, illustrating the diverse uses of the dark web and the continuing demand for online anonymity and security.
Access To The Dark Web
The dark web, a hidden layer of the internet not indexed by standard search engines, is often shrouded in mystery and misconception. Unlike the surface web, accessing it requires specialized software, configurations, and authorization. This article explores the practical methods and prerequisites for entering this obscure digital realm, focusing on technical steps and the overlooked aspects of gaining entry.
Essential Software: The Tor Browser
The most common gateway is the Tor Browser, a modified version of Firefox. To gain access to the dark web, users must download it from the official Tor Project website. This browser routes your traffic through multiple encrypted relays, effectively masking your IP address. Never use a standard browser like Chrome or Safari; they cannot connect to .onion domains, which are exclusive to the Tor network. Configuration is minimal—simply run the installer and start browsing.

The Onion Router Network
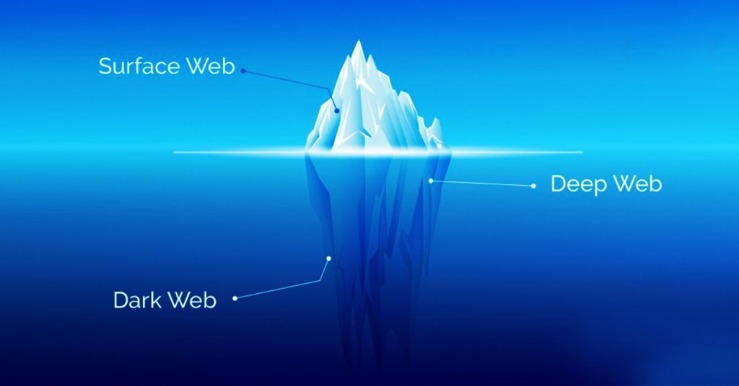
Accessing the dark web relies on the Tor network’s layered encryption. When you type a .onion URL, your data is encrypted in three separate layers, each removed by a different relay node. The final exit node decrypts the last layer and sends your request to the hidden service. This process ensures anonymity for both the user and the website operator. However, latency is significantly higher than standard browsing due to this routing overhead.
Alternative Methods: I2P and Freenet
Beyond Tor, other networks offer access to the dark web. I2P (Invisible Internet Project) creates a peer-to-peer overlay for anonymous communication, ideal for file sharing and email. Freenet focuses on decentralized storage, requiring users to contribute bandwidth. To use these, you must install their respective clients and configure firewall settings. Neither is as user-friendly as Tor, but they provide different security models for specific needs.
Security Precautions for Entry
Before pursuing access to the dark web, disable JavaScript in your Tor browser to prevent exploits. Use a VPN to add an extra layer of encryption before connecting to Tor—this hides Tor usage from your ISP. Avoid logging into personal accounts or downloading files, as they can compromise your identity. Never reveal personal information in forums or chats. The dark web contains both legal and illegal content, so vigilance is paramount.
Legal and Ethical Considerations
Simply accessing the dark web is not illegal in most jurisdictions, but your activities are. Law enforcement monitors public .onion sites for illegal marketplaces and forums. Using Tor for privacy is protected under free speech laws in many democracies, but buying contraband or viewing illicit material carries severe penalties. Always check local regulations before proceeding, and treat anonymous networks as tools for ethical research, not a shield for crime.