Compromised credentials are commonly sold on dark web marketplaces for use in credential stuffing attacks, where they test to see if the same password is used elsewhere as well. This focus on privacy means that the dark web is a popular forum for criminal content. On dark web marketplaces, these operators may sell control over bots or sets of bots to other cybercriminals looking to use them in their attacks. Botnet operators can have thousands of bots under their control and the ability to break their botnets up into smaller groups. Additionally, cybercriminals may offer access to corporate accounts for sale, allowing other attackers to purchase a foothold within an organization’s environment. Additionally, insider threats may put the organization at risk either intentionally or via negligence.
Access Darknet On Android
Accessing the darknet on an Android device requires specific tools and precautions, as the standard browser cannot reach hidden services. The darknet, a part of the deep web, is only accessible through specialized software like Tor, which routes your traffic through multiple layers of encryption. For Android users, this process is streamlined by official apps, but security and anonymity must be prioritized to avoid risks. Whether for privacy or research, understanding the correct setup is essential before diving into this hidden network.
Essential Apps for Access Darknet On Android
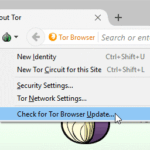
To access darknet on Android, you must first install the Tor Browser for Android from the official app store or the Tor Project website. This app is specifically hardened for mobile use, blocking scripts and tracking. Additionally, Orbot is a crucial companion app that acts as a proxy, forcing all data through the Tor network. Never use a standard browser for darknet access, as it exposes your IP address and undermines anonymity.
Step-by-Step Configuration
Since most people use the same password across multiple accounts, this method works disturbingly well. The rise of ransomware-as-a-service has made sophisticated password-stealing malware available to even novice attackers. You can crack passwords all day long, but why not trick users into just giving them to you? This is why modern systems use "salting" (adding random data to each password before hashing) to defend against rainbow tables.
After installing Tor Browser, open it and accept the default security settings. Avoid granting unnecessary permissions to the app, such as location access or camera use. When you access darknet on Android, you will encounter .onion URLs—these are the only way to reach hidden services. Always type or paste these URLs carefully, as mistyping can lead to phishing sites. For enhanced privacy, use a VPN before Tor, though this setup is debated among experts.
- So, the police started tugging at the threads to see where these phones lead.
- So, if I’m being real, features and functionalities really are the most important aspect of buying a phone for me, even though I’m so privacy-focused.
- This isolates your research from your primary systems and makes cleanup straightforward.
- Since receiving Tor Project support in 2014, Ahmia has maintained dual access points through both clearnet and onion interfaces.
- On Tor, you can type in any URL you’d like to visit, including .onion links on the dark web.
Risks and Precautions
When you access darknet on Android, be aware of malicious actors and scams. Do not download files from unknown sources, as they can contain malware that compromises your device. Use a secondary device or a dedicated profile solely for this purpose. Regularly update your Tor Browser and Orbot to patch security flaws. Never log into personal accounts while connected to the darknet, as this can de-anonymize you.
Testing Your Connection
To verify you can access darknet on Android correctly, visit a trusted check site like check.torproject.org from within the Tor Browser. If it confirms you are using Tor, you are ready. Bookmark a few reliable darknet directories for initial navigation, but always double-check their authenticity. Slow loading speeds are normal due to the multiple encryption hops required for anonymity.