Access Dark Web
Accessing the dark web requires a deliberate shift from the standard internet browsing experience. Unlike the surface web indexed by search engines, the dark web is a hidden layer of the internet that demands specific software, configurations, and knowledge to reach. Many people first encounter the concept through sensationalized news reports, but understanding the practical steps to access dark web environments is crucial for privacy advocates, journalists, and researchers alike. The process begins with downloading a specialized browser, most commonly the Tor Browser, which routes your connection through multiple encrypted relays to anonymize your digital footprint.
Essential Tools and Software
- Integrated control points to protect people and data, wherever work happens.
- The “S” in HTTPS stands for secure, and signifies that a website has an SSL Certificate and encrypts data traveling between your device and a website.
- This was notorious for buying and selling illegal drugs using digital currencies and was shut down by law enforcement in 2013.
- The online security practices of end users affect the safety of the entire business.
- It’s legal to access the dark web in the U.S. and most other countries.
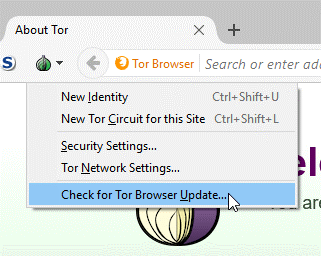
To successfully access dark web content, you must start with the Tor Browser, available for free from the official Tor Project website. This browser is a modified version of Firefox that automatically handles routing and encryption. Another tool, I2P (Invisible Internet Project), also facilitates access dark web but operates on a different peer-to-peer model. Beyond browsers, many users also employ VPNs (Virtual Private Networks) as an additional layer of security before launching Tor, though this can slow down connection speeds. Never use outdated software, as vulnerabilities in older versions can expose your real IP address when you access dark web sites.

Safety and Anonymity Measures
Common web search engines such as Google and Yahoo! use their own crawlers to collect and register information about websites on the Internet. It’s exactly the opposite of the Deep Web—that portion of the Internet that conventional search engines can index and standard web browsers can access without the need for special software and configurations. By implementing these measures, users can safeguard their personal information and enhance their overall security in this hidden part of the internet.

When you access dark web forums, marketplaces, or communication channels, your behavior is as important as your tools. Always disable JavaScript in the Tor Browser’s security settings to prevent tracking scripts and exploits. Avoid downloading files, as they may contain malware that breaks the anonymity layer. Use temporary email addresses and pseudonyms for any registrations, and never input personal identifying information. The phrase "access dark web" should remind you that operational security is non-negotiable—simple mistakes, like logging into a personal social media account while connected, can collapse your anonymity instantly.
Legal and Ethical Considerations
- Others have adopted a model called “extortion as a service,” where bigger gangs allow affiliates and allies to host stolen data on their sites.
- LastPass admins of LastPass Business accounts can manage the “Control dark web monitoring” policy and its settings.
- The anonymity and encryption provided by the dark web make it an attractive platform for these illicit activities, as it significantly hinders law enforcement efforts to track and apprehend the perpetrators.
- And you can only find many interesting and totally legal sites on Tor!
- When people go on about the so-called dark web, they're usually talking about onion sites, which aren't searchable via Google or accessible via standard browsers.
- But diving into the dark web blindly is dangerous you could stumble onto malware or illegal content.
While the act to access dark web itself is legal in most countries, many activities conducted there are not. Law enforcement agencies monitor hidden services, and accessing illegal content—such as unlicensed marketplaces or illicit material—carries severe penalties. Journalists and activists use the dark web to access dark web whistleblower platforms like SecureDrop, which is a legitimate and protected use. Always verify the legality of specific actions in your jurisdiction. A responsible approach to access dark web means staying informed about local laws and avoiding engagement with services that promote harm or fraud.
Finding Content and Hidden Services
Locating websites when you access dark web is not like using Google. Hidden services end in .onion domains and are not indexed by standard search engines. Directories like the Hidden Wiki exist, but they are often unreliable or contain traps. To safely access dark web resources, rely on reputable links shared within trusted communities or obtained from verified sources. Many access dark web guides recommend using search engines like DuckDuckGo’s .onion version to find legitimate forums, libraries, and privacy tools. Bookmarking reliable links is essential, as phishing sites often mimic popular .onion addresses to steal credentials.
Ultimately, access dark web environments demands respect for the technical and ethical boundaries that define this hidden network. Proceed with caution, verify every step, and remember that anonymity is a tool—not a shield for malicious behavior.