Tor, the decentralized anonymity network, has been an integral part of our workflows at The Intercept since we launched in 2013. Many free VPN providers lack basic security features and track your online activity, so they don’t offer much privacy. Fortunately, you can’t just stumble onto dark web websites by accident.
For iOS users, “Onion Browser” is a free and open source alternative to Tor Browser encouraged for use by the Tor Project. The shift toward interconnected digital environments has increased the surface area for potential data breaches, making encryption a vital tool for… With configurable user selection dialogs, it provides a user-friendly experience while maintaining strict security.
onion Dark Web
The .onion dark web is a hidden segment of the internet accessible only through specialized software, most commonly the Tor browser. Unlike the surface web indexed by Google, .onion sites obscure their IP addresses and location, offering a high degree of anonymity for both users and operators. While often associated with illicit markets, this encrypted network also serves critical functions for journalists, activists, and privacy-conscious individuals in repressive regimes.
How the .onion Dark Web Works

The infrastructure relies on onion routing, where data is encrypted in multiple layers and bounced through a series of volunteer-operated relays. Each relay peels off a layer of encryption, revealing only the next destination. This prevents any single node from knowing both the source and the destination. The result is a network where your activity is virtually untraceable unless you make critical operational security errors.
Legitimate Uses of .onion Sites
- Unlike emulated or simulated Tor browsers, which only mimic Tor's behavior, our platform provides full access to the real Tor browser and the Tor network.
- Tor .onion addresses use a specific subset of characters to encode their values.
- Tor browsers create encrypted entry points and pathways for the user, so dark web activity remains anonymous.
- For 2025’s world of pervasive surveillance and cyber threats, blind faith in anonymity is dangerous.
- Whistleblowing platforms like SecureDrop allow sources to submit documents without exposing their identity.
- Anonymous browsing for journalists researching sensitive topics such as corruption or human rights abuses.
- Censorship circumvention in countries that block news websites or social media.
- Privacy-focused email services that do not log metadata or IP addresses.
Risks and Illicit Activity
The anonymity of .onion also attracts illegal enterprises. Darknet markets trade drugs, stolen data, and weapons using cryptocurrencies. Hacking forums offer exploits for sale, while some sites host illegal content. Law enforcement agencies actively monitor and take down these services, but new ones constantly emerge. Users should be aware that merely visiting some .onion sites could be illegal in certain jurisdictions.
FAQs about the .onion Dark Web
Q: Is the .onion dark web illegal to access?
A: No, using Tor to access .onion sites is legal in most countries. However, engaging in illegal activities on them is not.
Q: Can I be tracked on a .onion site?
A: While Tor provides strong anonymity, it is not infallible. Advanced attacks, JavaScript exploits, or user mistakes can compromise your location.

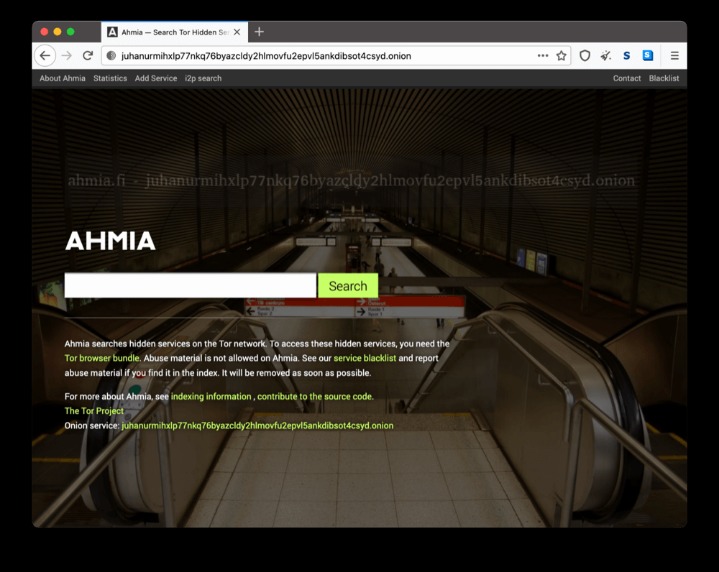
Q: How do I find .onion websites?
A: Unlike the surface web, there is no central search engine. Directories like The Hidden Wiki list some, but many are shared via QR codes or encrypted forums. Always verify sources to avoid scams or phishing sites.
Key Tools for .onion Navigation
- Tor Browser – the essential tool, based on Firefox, pre-configured for anonymity.
- Tails OS – a live operating system that leaves no trace on the computer.
- Orbot – proxies apps through Tor on mobile devices.
- Bridges – hidden Tor relays used to bypass censorship in restrictive countries.