It’s also the default search engine in Tor Browser, which keeps it widely used in privacy workflows. DuckDuckGo was founded in 2008 and has been usable through Tor since 2010, later introducing a modern v3 onion service in 2021. Final selection was based on how well each engine fits real dark web research and monitoring use cases. Deep Search claims to be built by students who created a new powerful Tor search engine.
onion Link
The .onion link is a specialized top-level domain suffix used exclusively on the Tor network, designed to provide anonymous and encrypted access to websites. Unlike standard domains like .com or .org, a .onion link cannot be accessed through a regular browser—it requires the Tor Browser or a similar proxy configuration. Created from a cryptographic hash of a public key, each .onion link ensures that the server’s location and identity remain hidden, offering a unique layer of privacy for both operators and visitors.
The Technical Foundation of a .onion Link
Every .onion link is generated through a process that derives a 16-character alphanumeric address from a public keypair. This address, such as example123456789.onion, acts as both a routing identifier and a verification token within the Tor hidden service protocol. When a user types a .onion link into the Tor Browser, the network uses a distributed lookup table to locate the service without revealing the original IP address. This architecture makes the .onion link inherently resistant to censorship and surveillance, as no central authority controls its registration.
Why Use a .onion Link?
Organizations and individuals deploy .onion links for a variety of reasons, from protecting whistleblowers and journalists to enabling secure communication in repressive regimes. A .onion link prevents traffic analysis by encrypting data multiple times as it passes through three or more relay nodes. For example, The New York Times operates a dedicated .onion link to allow readers in countries with strict internet filters to access news safely. Additionally, law enforcement agencies use .onion links for anonymous tip lines, while some activists run forums or blogs exclusively via .onion links to evade monitoring.
Risks and Misconceptions
- A Tor hidden service (sometimes called an “onion site” or an “onion service”) has a special domain name that ends in .onion – like p53lf57qovyuvwsc6xnrppyply3vtqm7l6pcobkmyqsiofyeznfu5uqd.onion – that you can only connect to using Tor.
- Dark web websites are pages that exist on a part of the internet that isn’t indexed by traditional search engines like Google.
- Riseup is an invite-only email and communications service that doesn’t hold onto any of the data you generate when you use it.
- Explore our penetration testing services to see how we can uncover vulnerabilities before attackers do.
- Although many use the dark web for privacy, some Tor websites also let people connect with others.
- Additional features like market and forum search capabilities, API access, and regularly updated directories enhance the safety and efficiency of navigating the dark web.
Not all uses of a .onion link are legitimate; the same anonymity that protects human rights defenders also enables illegal marketplaces and forums. However, claims that every .onion link is tied to criminal activity are misleading. The hidden nature of a .onion link does not automatically imply illegality—it is a tool, not a moral statement. Users should exercise caution, as visiting an unverified .onion link can expose their system to malware or phishing attempts, especially if the site demands personal data.
How to Access a .onion Link Safely
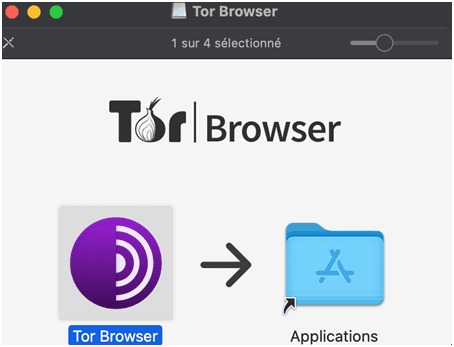
To visit any .onion link, download the official Tor Browser from the Tor Project’s main website (using a non-.onion link for initial retrieval). After installation, simply paste the .onion link into the address bar—the browser will handle routing. Never enter personal login credentials on an unknown .onion link, and avoid enabling JavaScript unless absolutely necessary. For maximum security, consider using a VPN in conjunction with the Tor network, though this may degrade speed. Always verify a .onion link’s authenticity via secondary sources, as fake mirrors of popular services are common.
The Future of .onion Links
With the rise of decentralized web protocols and encrypted DNS, the .onion link remains a critical tool for privacy. The Tor Project continues to improve the usability of .onion links, including support for next-gen v3 addresses (56 characters long, more secure than v2). As governments tighten internet controls, the .onion link may become a standard fallback for mainstream sites. For now, understanding how to navigate this hidden web is a valuable skill for anyone prioritizing digital autonomy.


